One of the big things I have been working on is working towards getting more PoPI Complaint. Although there is not a specific set way of doing this, the main thing I read up, and spoke to different more Knowlagable people regarding this is that Reasonable steps need to be taken to prevent data being stolen. As well, if data is stolen that again Reasonable steps need to be in place to make sure the data is Unusable.
So how do you make data unusable if your devices get stolen? The Simple answer is encryption. But it is very much possible when you bought your Laptop this was not on your list of questions, and now you have laptops without the required Hardware (TPM) to implement Bitlocker Encryption.
Well, don’t stress there is a way to still encrypt your Windows Machine without the TPM Module.
Group Policy Editor
For this to work you will need to be an administrator on your machine. These policies can be pushed down from the Group Policy Manager on a Domain setup but the below is done on a Non-Domain Joined Machine.
Start clicking on the start button and typing gpedit.msc. This should bring up a Microsoft Common Console Document. If not open a run Command and simply type gpedit.msc and ok to open MMC.

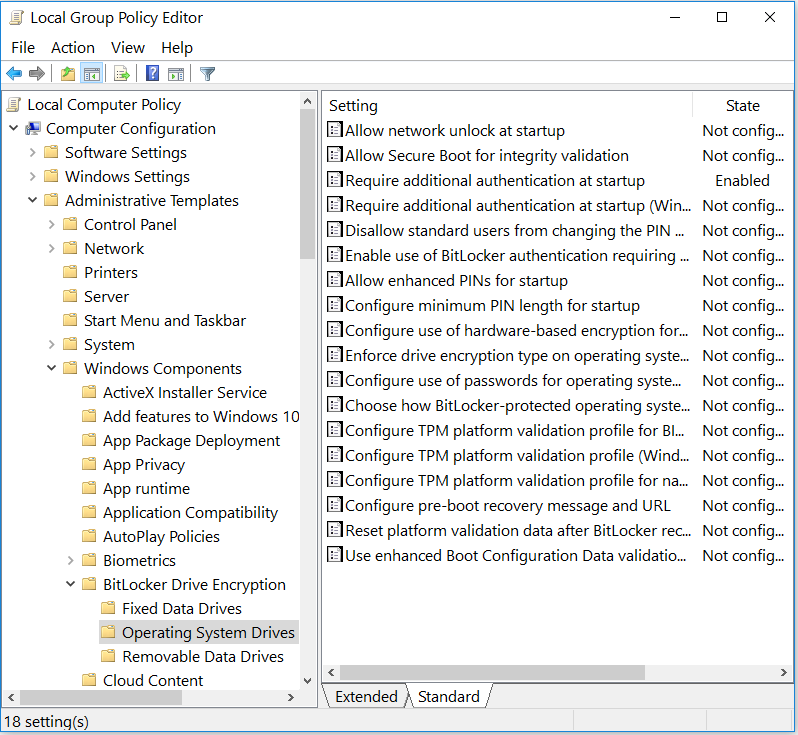
Once the MMC is opened you will see a Similar screen as per below screen capture. Browse to:
Computer Configuration > Administrative Templates > Windows Component > Bitlocker Drive Encryption > Operating System Drives
The Setting you are looking for is:
Require additional Authentication at Startup
Edit the setting by choosing Enabled and make sure you tick the:
Allow Bitlocker without a compatible TPM
(Require a Password or a Startup Key on a USB Flash drive)
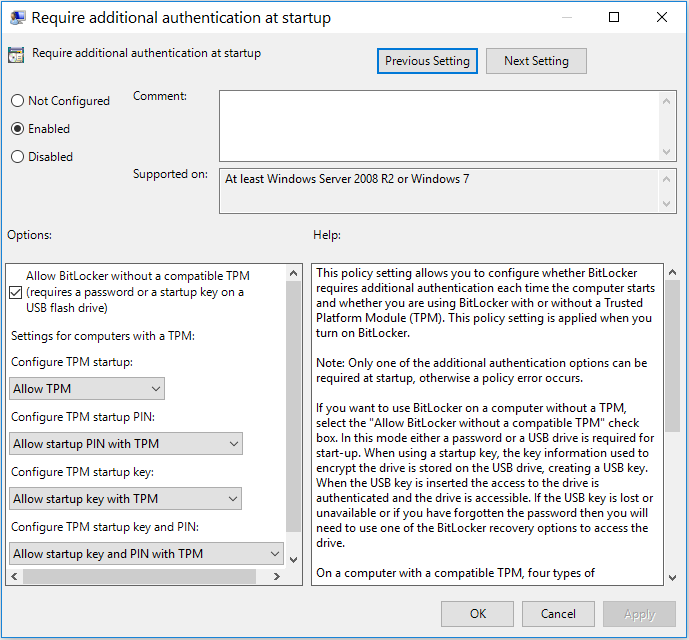
Click ok and close all windows. You are now ready to enable Bitlocker.
Setup Bitlocker
Open the Control Panel and search for the option Manage Bitlocker.
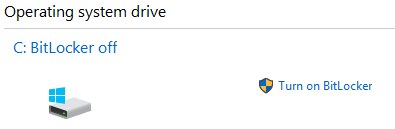
On the Drive, you want to enable click Turn on Bitlocker.
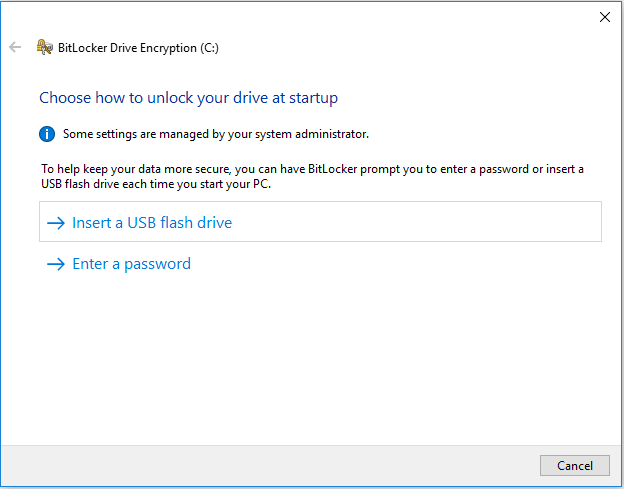
It will go past the point where it says you don’t have TPM installed and instead give you an option to use a USB Flash Drive or a Password.
I do Caution if you are a person that losses Flash Drives, don’t use this option. As this is a virtual environment I am working on I opted for Enter a Password
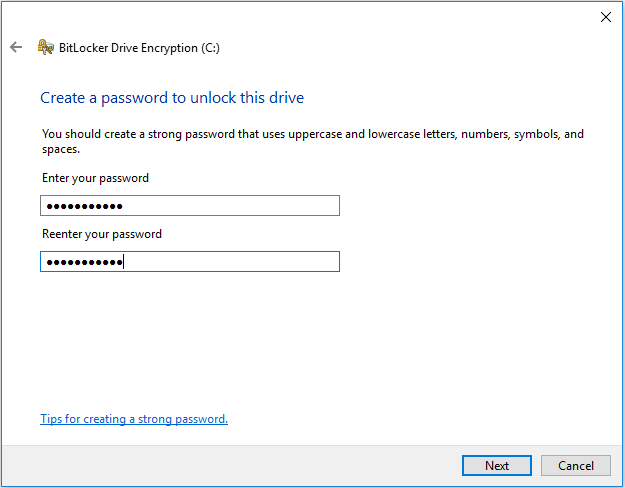
The password needs to be somewhat complex. Try using Good Practice Techniques.
Don’t use a password you used before.
Don’t use a password that is personally identifiable
If you have a Password Manager that can generate Passwords use it.
Don’t write the password on a Note (Ever)
Once you have entered a password click Next.
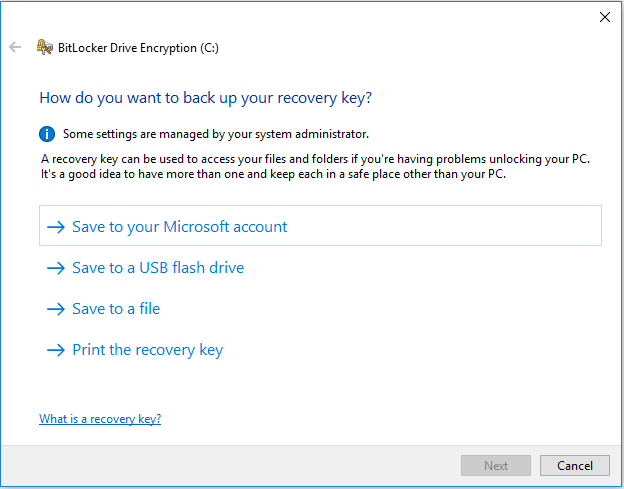
This is probably the most important after choosing a password. Save the Recovery Keys. This needs to be a secure location. NOT WITH THE DEVICE.
If you ever forget your Password or Lose your Flash Drive this is the only way to retrieve the data on the Hard Drive.
For the smart people out there saving their Data to the Cloud, I get it you have your Data. This is for Unlocking the Hard Drive.
If you’re managing a Domain you can setup the Policies to backup the Recovery Keys while setting up the Encryption.
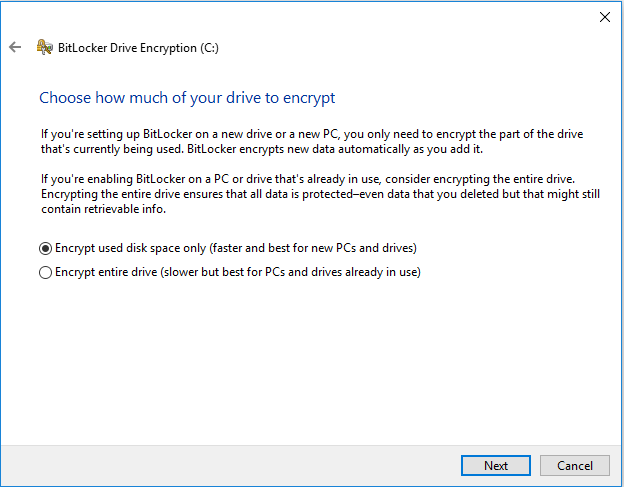
Once you saved your Recovery Keys you can then choose how to encrypt.
I suggest choosing the Entire Drive.
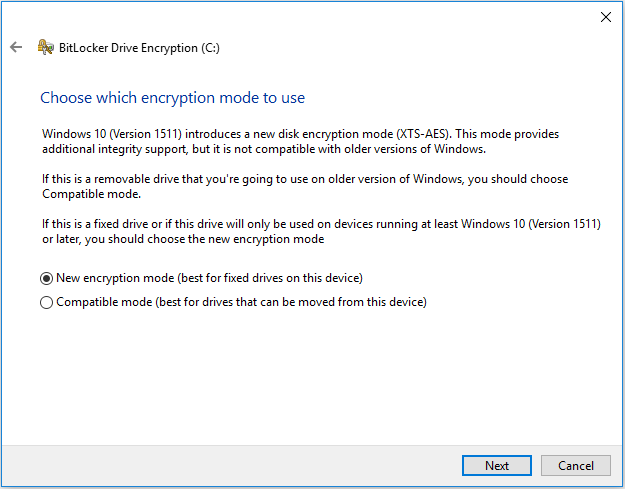
Lastly, choose which encryption type you want to run. Basically, if the drive is not installed in the Device choose Compatible otherwise choose New encryption Mode
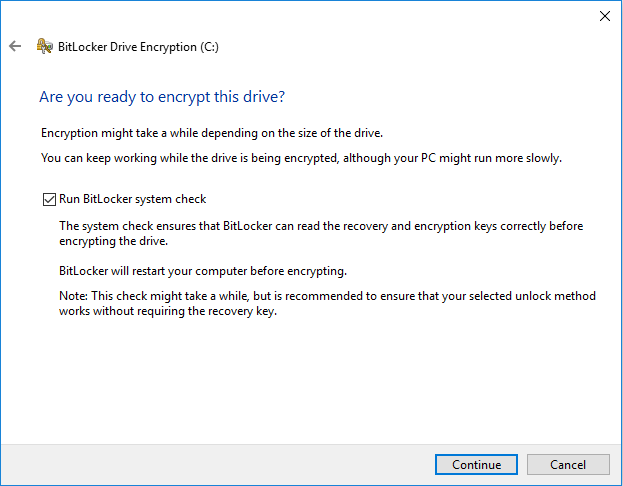
Once Done finish the Encryption Setup by Clicking Continue to process.
It Worked
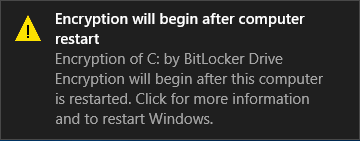
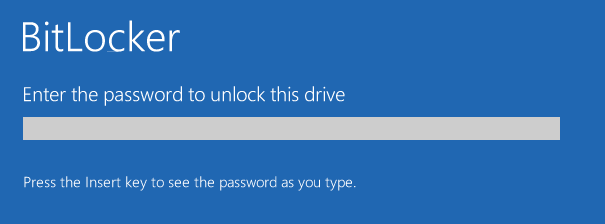
The Device will need to rebooted to start the Encryption. On the Reboot, it will request the password you set for the Encryption.
If you typed everything correctly once you are back in windows you will see the progress of the drive encryption.
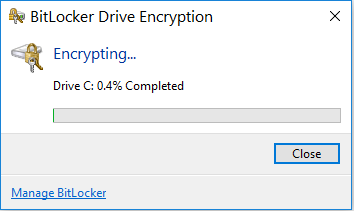
While Encrypting you will have a slight performance issue but most people barely notice this.
