So I am working on a project to get all the LogOn \ LogOff events for a specific user on a Terminal Server.
When I did few online searches there was some indication of how to get this done with PowerShell.
But this did not have exactly what I was looking for because it only specified Log On and Log Off event.
What happens if the user disconnects and Reconnects, does this also count as a Log Off Event?
I am looking for a list in csv forma which will give me the Instance ID (converted to reading Format) with the User Name and the Time of the event. Seems Simple Enough.
Event Viewer
To do the necessary I looked at the Event Viewer and Compared the output to PowerShell.

To get to the event viewer open the Start menu and type in Event, alternate Click the Icon and select run as administrator.
Once Open Browse to the Security Event Log and filter the log by Instance ID 4624. This will give you the Full view of the Event Logged. The Event Viewer gives a very fair amount of data but there is one very critical Section Missing.
There is no User Name at all.
Power Shell
Doing the same with Power shell we get the exact same issue, No User Name.
 As well is now the Category is numbers instead of Human Readable Format.
As well is now the Category is numbers instead of Human Readable Format.
To get the Full PowerShell view of the event Open PowerShell in Admin Mode and Copy and Paste the Below commands.
$Event = Get-EventLog -LogName Security -InstanceId 4624 -Newest 1
$Event | Format-List
Power Shell VS Event Viewer
Below is the link between the data that I could best fit.

The Table shows the information received from PowerShell against what shows in the event viewer. (NA = Not Available)
| Power Shell | Event Viewer | |
| LogName | NA | Security |
| Index | 13400 | NA |
| EntryType\KeyWords | SuccessAudit | Audit Success |
| InstanceID\Event ID | 4624 | 4624 |
| Message: | Very Long Text | NA |
| Category: | (12544) | NA |
| CategoryNumber | 12544 | NA |
| ReplacementString | Coma Seperated List | NA |
| Source | Microsoft-windows-Security-Auditing | Microsoft Windows Security |
| Time Generated | Time and Date Given | NA |
| TimeWritten\Logged | Time and Date Given | Time and Date Given |
| UserName | Blank | Not Available |
| Level | NA | Information |
| OpCode | NA | Info |
| Task Category | NA | Logon |
| Computer | NA | Computer Name |
So how does the Event viewer have information that PowerShell does not?
Well the Replacement string is the answer, the event viewer reads the information from this comma separated list and populates the Computer field.
So my question to Microsoft, Why could you not just populate the Username as well?
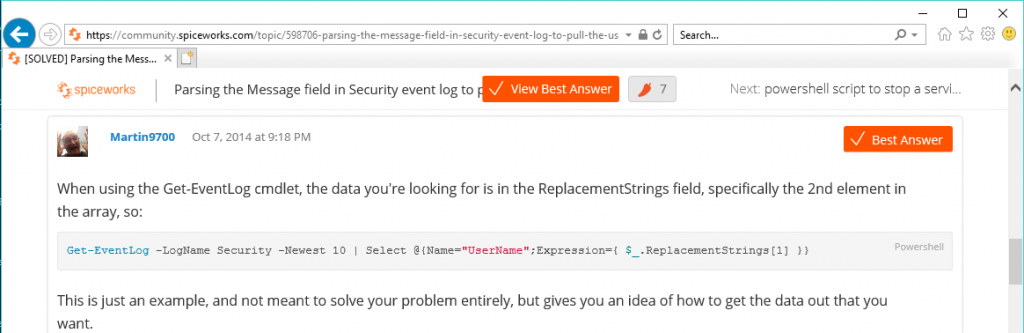
Anyway to get past this we have to modify the code to read the replacement string.
See Post: Power Shell Replacement String Variables for more details
I have to say thanks to Martin9700 on Spice Works for assisting with getting the answer:
So Solving one question does not resolve the query yet as more questions was created.
- What InstanceID do I need to Search for?
- How do I convert the Category back to Readable Format?
Look out for the next Post to see how we resolve Each Question.
