So I decided to download Server 2019 and mess around with it but let me do it in Command-Line. Something that I have never done before.
I got to installing the AD and realized I have to do a brush-up on the High Level of AD.
What is an Active Directory
Active Directory is a Microsoft Created Technology used to Manage Network resources. It is an authentication and authorization process of Logical grouping.
Basically, in my view, Active Directory is a Single Sign-on that gives your resource access to Exactly what it needs. It also denies access to everything else and it is done in large scale. This makes changes in Minutes instead of over Months. Don’t misunderstand me there is a lot of other functionality AD brings with it like “Centralized Group Policies” and “Exchange Integration”. But first and foremost it is an authentication service that allows single Large Scale changes to groups of Resources.
What do you get in AD
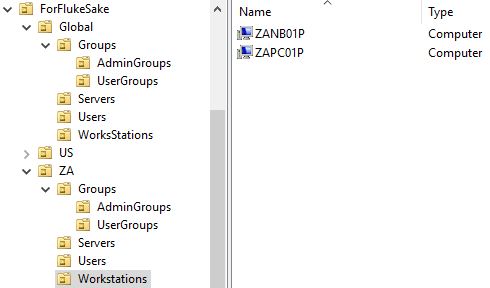
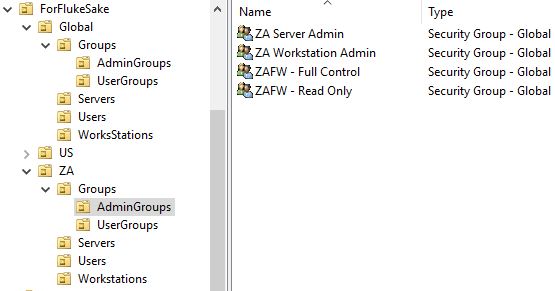
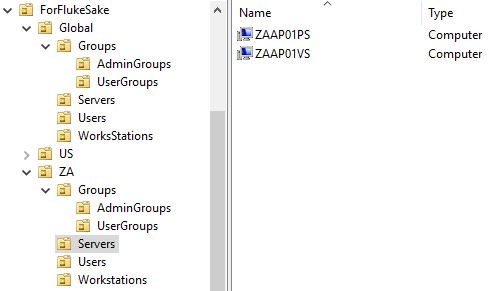
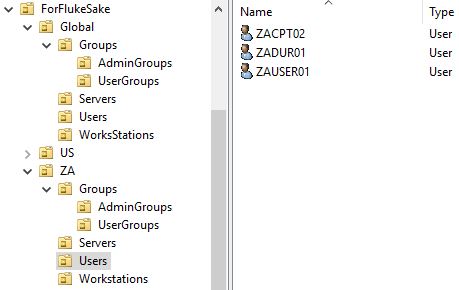
Kicking off with Users and Computer each User and Computer is a unique Physical\Virtual resource. Which is why the AD was created because they get too much to Manage. Each resource can then be added into their Respective Groupings with each group giving the resource Specific access rights. A Resource can be a member of multiple groups.
What meant with Virtual User? Well, this is Generic accounts or Service Accounts, accounts used for a specific purpose but not by a specific Person.
Groups are created to bulk manage Service Resources. A Service Resource is anything like the access to a Firewall Terminal to Shared Folder Access and who can log into an application. Before the Service Resource gives you access it will query the Domain Controller confirms the Physical\Virtual Resource has access and then either deny or allow depending on the result it receives back.
Then there is OU or Organizational units which are for Administrative purposes. A Computer OU Called “Level 1 – Workstations” will automatically have USB access and a “Level 2 – Workstations” will be Denied Access. Having a user in the ZA_OU will set their Time to South-African Date Time compared to United State Date Time in the US_OU.
This all forms part of the Domain which is hosted on Servers called Domain controllers. The Domain Controller holds the Schema for the Active Directory which is extendable with additional features like Exchange.
What about Multiple domains?
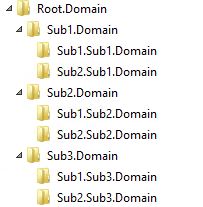
Active Directory can easily be expanded for the Right Situation. A small company which does not require multiple domains you can keep to one Domain. The time I have been in IT this is the only one I ever worked with. But if you require to branch out due to various reasons the AD allows to Create Subdomains. These are called Trees. I think the simplest way to remember this is to think of it as the tree structure you get on the right side of your Windows Explorer. Your Drive would be the main domain and all sub-folders will be Subdomains. In the tree structure, all Sub-domains automatically trust one another due to all of them trusting the Main domain. This is called Transitive trust or Two Way Trust. In short “A Friend of a Friend is my Friend”.
Keep in mind this is not the case with all trusts.
In bigger companies where one company would acquire another company a one-way trust can be set up between the Two different Domains or Trees, this is known as a forest and the trust is an explicit trust or a one-way trust.
It should be noted when creating your first domain you are technically creating a tree and a Forest as all the piece is already in place to add or Merge with other domains, but by merging with another Domain you still only have one forest.