DMARC is one of those Technologies which sees the benefits of other Technologies and Goes: Hey, What you are doing is awesome, but let’s combine and do it better!!! In a nutshell, DMARC assists with Mail Security and Mail Deliverability for the Sender and the Receiver.
If you don’t know what I am referring to you can read up on SPF and DKIM. If time is limited let me do a quick Recap for you.
SPF
With Sender Policy Framework( SPF for Short) the receiving mail server contact the authoritative domain and Says “I just received this mail claiming it has permission to send on your behalf, here is the location it came from” and the authoritative domain then replies either Yes that is a trusted location or No I don’t Trust that location. Which allows the receiving domain to decide what to do with the mail.
DKIM
DomainKeys Identified Mail, on the other hand, gets singed with a digital Signature when leaving the Sending Domain Server. On the Receiving domain server, it contacts the Signing Domain where a public key is kept. It then uses this key to confirm the mail was not tampered with in transit. And again this allows the receiving domain to decide what to do with the mail.
How is this not enough?
Well, there are always people out there that understand technology better than us and they found ways to trick these technologies to think it is work. Now don’t get me wrong I am not saying all technologies if Full Proof if it was we would not have so much Anti-Virus update or Microsoft updates.
For Example with SPF what if your Server is hosted in a Shared environment like Office 365 of the GSuite, although you have limited the threat it is still in the location where thousands of other domains are hosted. And if DKIM does it signing on certain sections of the the mail one can easily tamper with the unsigned section and still get the same result.
Thus DMARC was created.
What is DMARC?
Like both the above two mentioned Technologies there are two sides to this:
The Sending Domain specifies how much of the mail needs to pass verification and what needs to happen to the mail depending on the result
The Receiving Domain can choose to follow the Sending domain specifications or not.
Confused?
So think of it like this, you sent a mail to a third party. The mail leaves your Mail server and gets signed with the necessary DKIM key that is added to the header. The receiving mail server then on receival first check that the server that sent it has the permission to send it. This is done using the return-path section in the header. It then takes the Signing domain (d=”Value”) from the DKIM section of the Header and validates it to see if tampering did not take place. Let’s say both of them returned with a Passcode.
DMARC then takes both the return-path and the d=”Value” and test for alignment.
What is the alignment? Both these values get compared to the “from” address in the email if the domain Matches then it is aligned and if not then it is not aligned. Each one’s alignment gets tested separately.
Now you can specify in the Record you are going to create if the alignment should be relaxed or strict. Depending on the result you want you then specify to the receiving mail server what it should do to the email.

Relaxed vs Strict
In relaxed mode, Sub-domain is treated the same as top-level domains. For example, if you key would be d=”example.com”, then emails from both test@example.com and test@new.example.com would both pass alignment. With strict mode, test@new.example.com would fail alignment.
Reporting
Before getting into the setup it is very important that you understand DMARC is not something you set up quickly and expect everything is working you can easily stop legitimate emails from being delivered because you don’t have a clear overview of where the company’s emails are being generated.
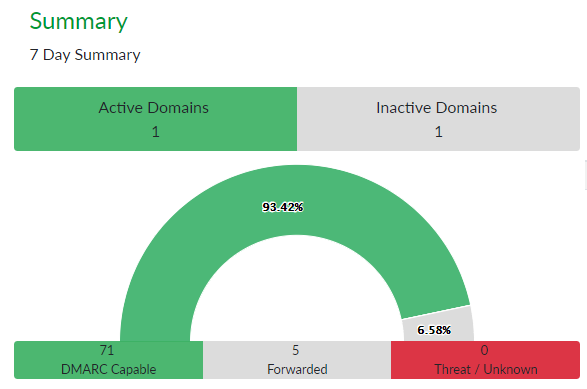
This is where the reporting you receive back is very useful. Servers that use DMARC response back every set amount of hours on all emails received to the sending mail domain. Now you start to see which servers are using the company domain and to which locations it is being sent. It also shows you how many of those emails the SPF, DKIM, and Alignment passed on. These reports do get technical very fast but luckily there are providers like https://dmarcian-eu.com that assist with quickly getting the information into a neat and readable format.
See below example of the dmarcian dashboard:
Finally the setup
There are two ways of doing the setup.
- Get an online tool to assist, I used dmarcian and it takes you step-by-step what each section does and what you can configure.
- Setting up the record manually as this is much more work it gives you a better understanding of the technology.
Regardless
Regardless of which one you choose I suggest setting up DMARC to monitor only for at least a month and then systematically moving to quarantine and the rejection in small intervals at a time.
Manual
DMARC is a DNS txt record type, set up on the authoritive domain. The Name of the record would start with “_dmarc” and end with “.mydomain.co.za”. Example: _dmarc.forflukesake.co.za.
The Value can range have a range of different properties, if a setting is omitted it will pass a default setting for a full breakdown of the setting see DMARC Settings
See below example:
v=DMARC1; p=none; rua=mailto:fluke@forflukesake.co.za; ruf=mailto:fluke@forflukesake.co.za; fo=1; sp=none; ri=86400;
This would monitor the results of all emails but not do anything with it, this is purely to receive back information on your environment so that the necessary changes and configs can be done to get the pass rate as close to 100 % as possible.
Once you are at a high-level pass rate you would change the setting to:
v=DMARC1; p=quarintine; pct=10; rua=mailto:fluke@forflukesake.co.za; ruf=mailto:fluke@forflukesake.co.za; fo=1; sp=none; ri=86400;
Now it will start quarantine (Spam) mail that is not following DMARC on a sample group of 10. So only 10 of every 100 mails will be checked.
You can add and remove properties as you require but I suggest having a set time between test to confirm if it is better for your environment or not.
Below is a breakdown of Tags I used and what each Tag is used for.
| Tag Name | Purpose | Sample |
| v | Protocol version | v=DMARC1 |
| pct | Percentage of messages subjected to filtering | pct=20 |
| ruf | Reporting URI for forensic reports | ruf=mailto:authfail@example.com |
| rua | Reporting URI of aggregate reports | rua=mailto:aggrep@example.com |
| p | Policy for organizational domain | p=none, quarantine, reject |
| sp | Policy for subdomains of the OD | sp=reject |
| adkim | Alignment mode for DKIM | adkim=s Relax or Strict |
| aspf | Alignment mode for SPF | aspf=r Relax or Strict |
