In a previous post, I wrote about How to setup Bitlocker without TPM. Now let’s just suppose you work in an environment where you have multiple IT People managing Multiple Laptops. If even one person does not save the Recovery Keys where it is supposed to be you potentially could lock yourself out of a Drive. A better way of doing this is to Backup Bitlocker Recovery Key to AD DS.
Now, this is a three-step approach:
- Get your AD Ready to accept Recovery Key’s
- Setup the Group Policy’s to Force Backup
- Setup Bitlocker
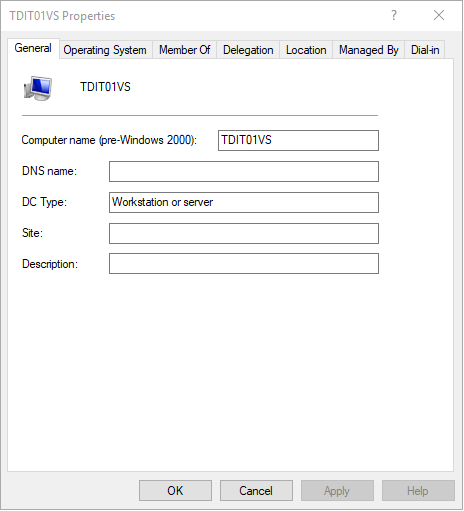
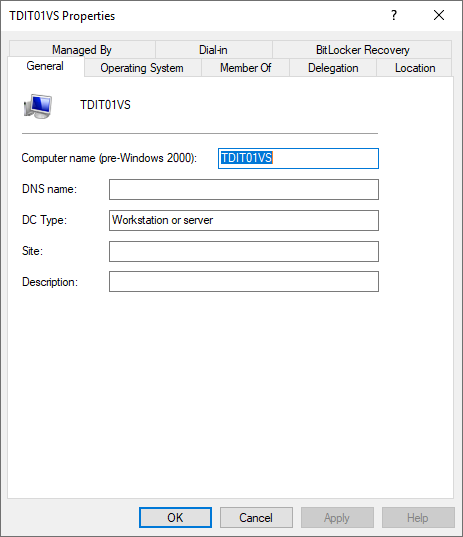
Before we get the AD ready first look at any Computer Properties in the AD Users and Computer. As per below, you can not view if the Bitlocker Key’s have been backed up.
Get your AD Ready
AD DS Schema
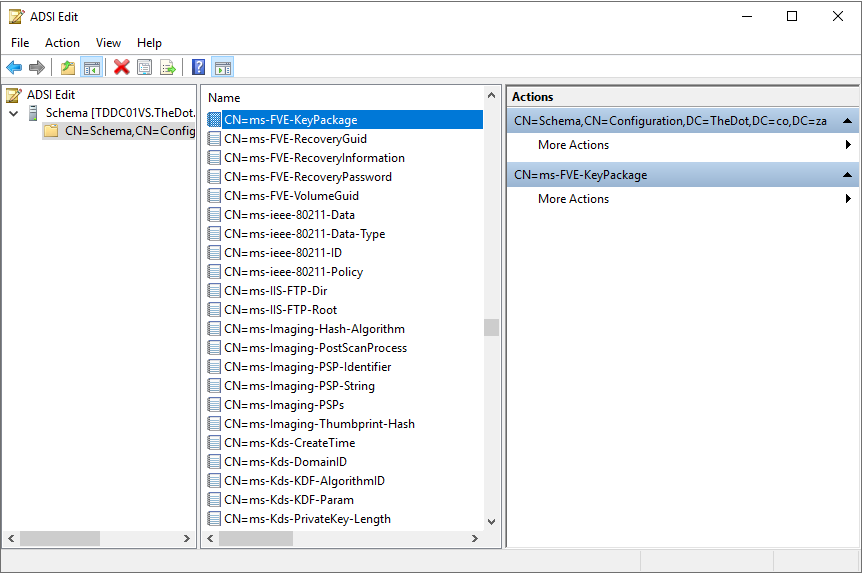
So First we need to verify that the server schema has been extended to support Bitlocker Recovery Keys. The Five scheme values are:
- ms-FVE-KeyPackage
- ms-FVE-RecoveryGuid
- ms-FVE-RecoveryInformation
- ms-FVE-RecoveryPassword
- ms-FVE-VolumeGuid
To see if the schema has been extended you can use the below two techniques.
Powershell
In Powershell simply paste the below command:
Get-ADObject -SearchBase ((GET-ADRootDSE).SchemaNamingContext) -Filter {Name -like "ms-FVE-*"} | Format-Table -Property Name
ADSI
Alternatively, click on the Start button type in ADSI and open ADSI Edit. Right Click ADSI Edit and choose to connect. In the Known naming Context make sure to choose Schema.
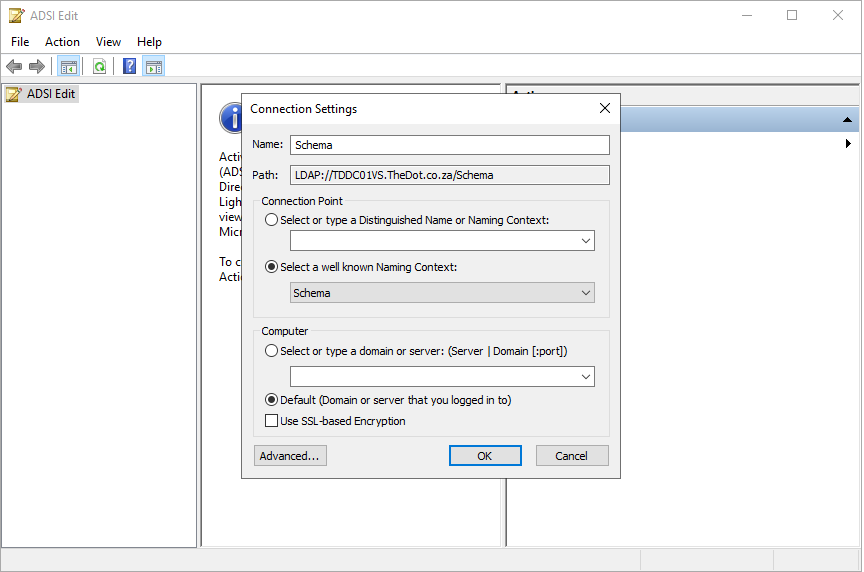
Simply browse down until you find the keys.
Schema Missing
As per Microsoft, all the schema should be there is you are running Server 2003 SP 1 or newer. If the schema is missing you can use the below command to extend the schema. For more information on this Click Here
ldifde -i -v -f BitLockerTPMSchemaExtension.ldf -c "DC=X" "DC=YourDomain,dc=com" -k -j .
You need to fill your domain details at: DC=YourDomain,dc=com
If you are not sure what should be filled in. go to Active Directory Users and Computer. Right-click the Domain Name and choose Properties. Then go to the Attribute Editor and Copy the distinguishedName value.
Just in case your Attribute editor does not show, click on View and choose Advanced Features in the AD Users and Computer Panel.
Add Roles and Features
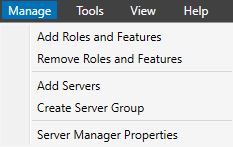
Next open your Server Manager, go to Manage and Add Roles and Features.
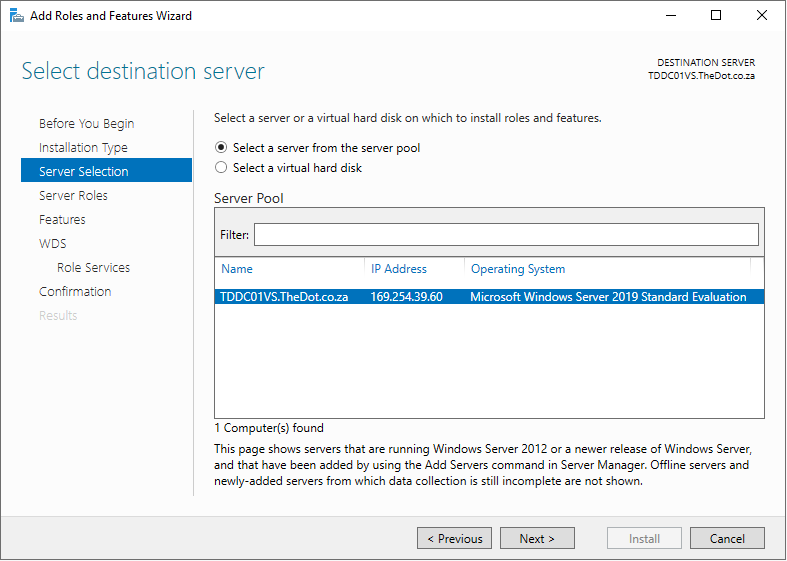
Click next until you get to the Server Selection and make sure you choose the which has Domain Services installed.
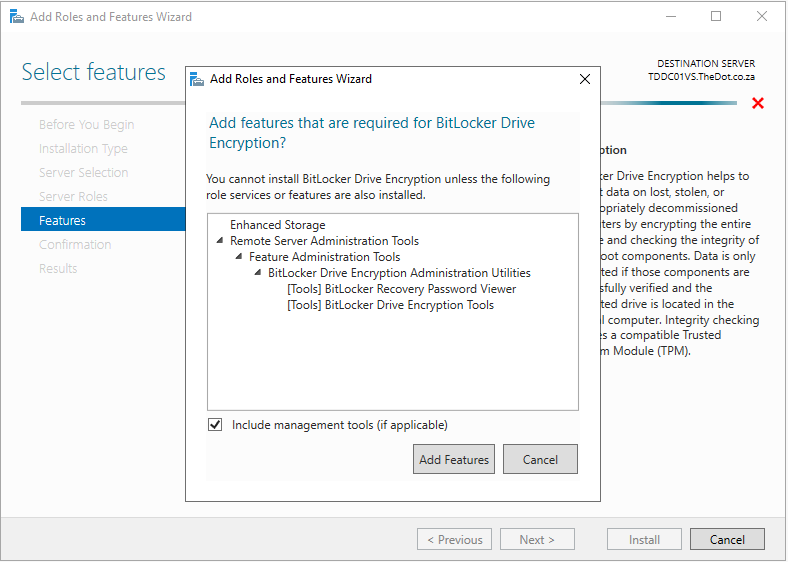
At the Feature Selection choose Bitlocker Drive Encryption and add the features.
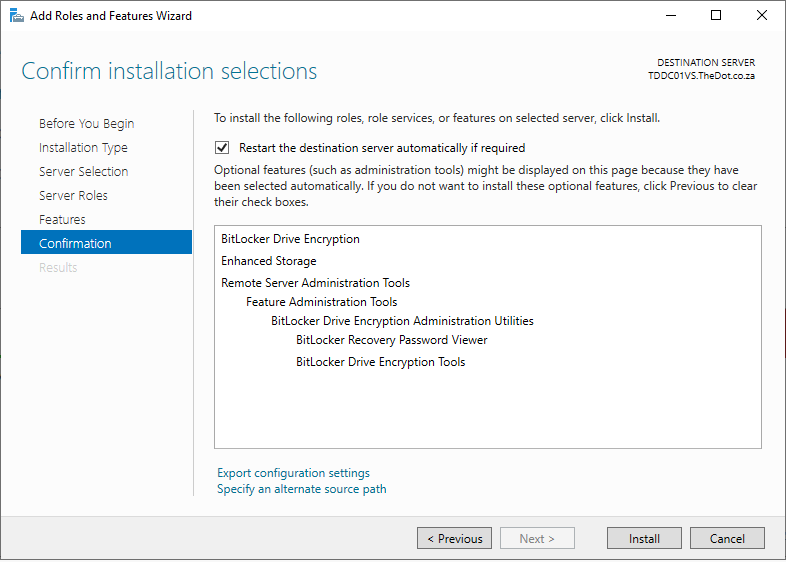
Continue on until you can install the required Features. Note the server does require a reboot on completion.
Once the server rebooted, go back to the Computer properties in AD Users and Computers. You should have and Extra tab now for Bitlocker Recovery.
Delegate AD Permissions
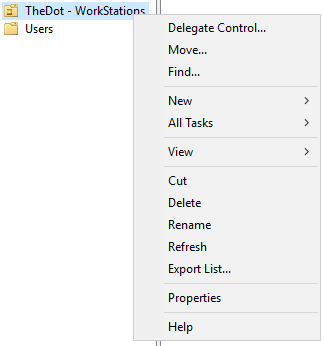
The last step to get your server ready is to Delegate permission to allow writeback from the device. To do this go to the location on the AD User and Computers where the devices that you will be enabling Bitlocker on are kept. Right-click the OU and choose Delegate Control.
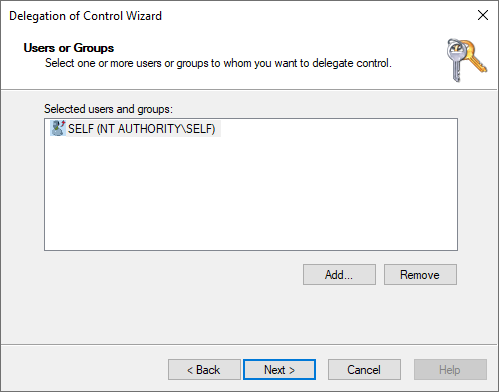
At the Users or Groups Click Add… and add the Self. It should look similar to below.
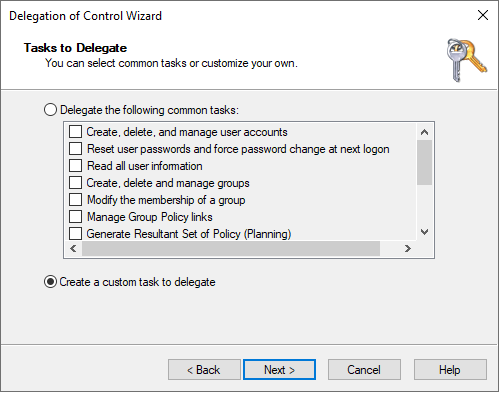
On the following screen choose Custom Task and Next.
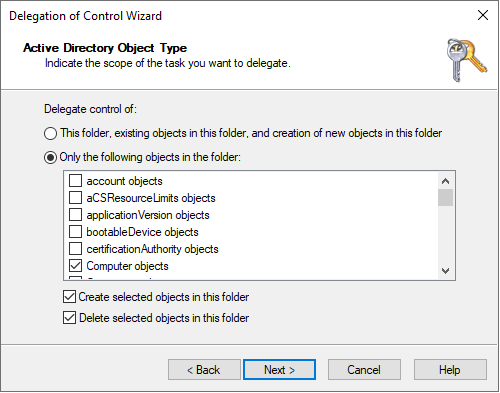
Choose Only the following objects in the folder and tick both the options for: Create selected objects in this folder and Delete Selected objects in the folder
For the Permission page Tick only, Property-specific and then in the permissions scroll down to Write msTPM-OwnerInformation
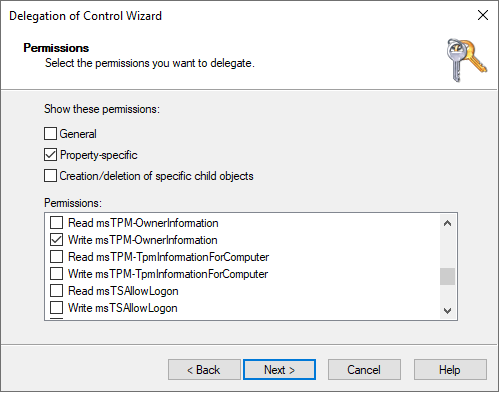
Click Next and Finish to complete the Delegation.
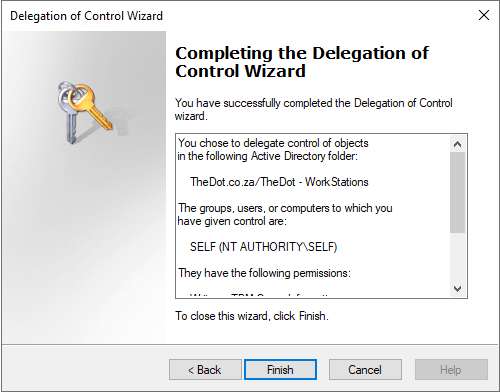
This is it if you did not receive any errors you AD is ready to receive Recovery Keys. Next, we need to set Group Policy’s that tells the machine where to store the Recovery Keys.
