Continuing off the previous post where we got the server Ready to Backup Bitlocker Recovery Keys. We now reached the point where we need to push down the Group Policies to the client devices.
Just a Reminder this is a Three-Step approach:
- Get your AD Ready to accept Recovery Key’s
- Setup the Group Policy’s to Force Backup
- Setup Bitlocker
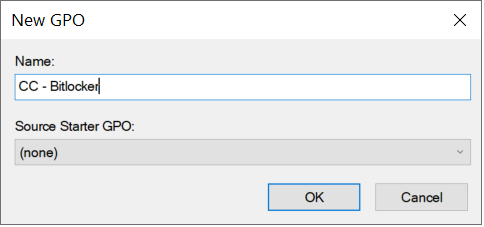
Creating the Policy
From the Server Management open the Group Policy Management Console. Browse to the location where the Devices are located that will be Bitlocked and Create the New GPO.
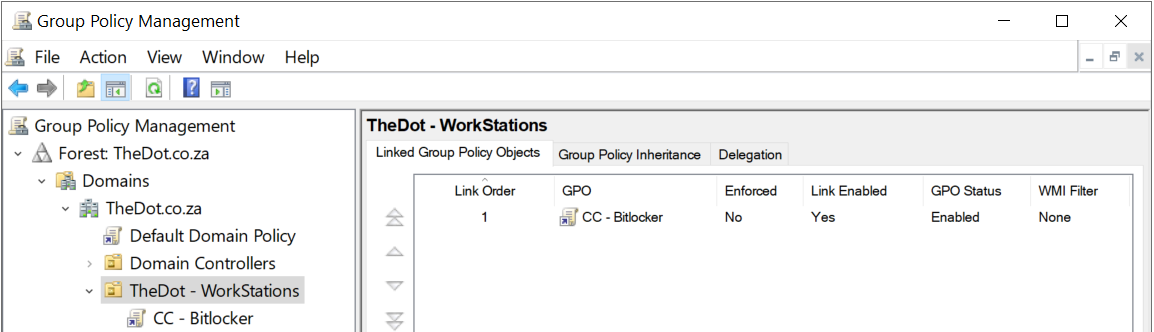
This will be pushed down on the Computer Level thus I named my GPO:
CC – Computer Configuration
Bitlocker – The Specific function of this GPO
I always suggest a Name that is identifiable. If you have to guess what the Policy does troubleshooting gets difficult. Aswell, Even though there are debates on which way are better. I prefer to split the GPO’s everyone has a Specific Purpose. This way it troubleshooting every occurs you know exactly where to start.
Edit the Policy
Once done you can edit the policy and browse to the following Location:
Computer configuration > Policies > Administrative Templates > Windows Components > Bitlocker Drive Encryption
In the root folder, the first option is:
Choose how users can recover Bitlocker-protected Drives (Windows Server 2008 and Windows Vista)
Please note this option only works for Windows Server 2008 and Windows Vista
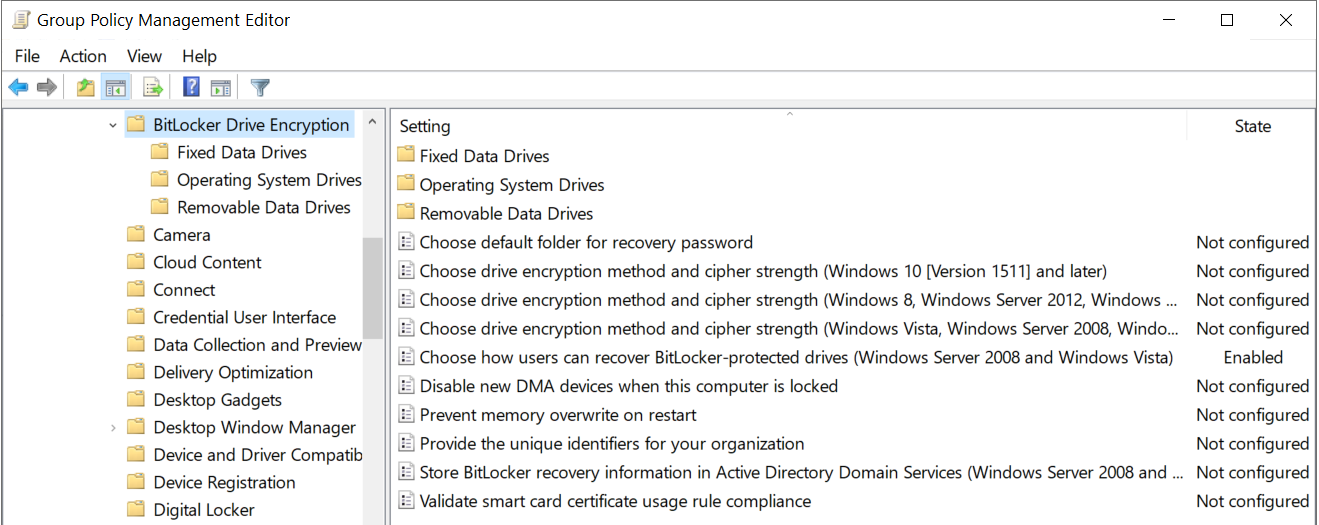
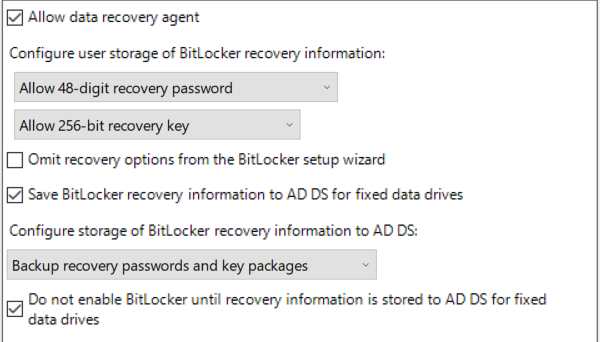
For all other Operating systems, you will set the settings as per below. With Emphasis on making sure you tick the very last option:
Do not enable Bitlocker until recovery information is stored to AD DS for #### Data Drives.
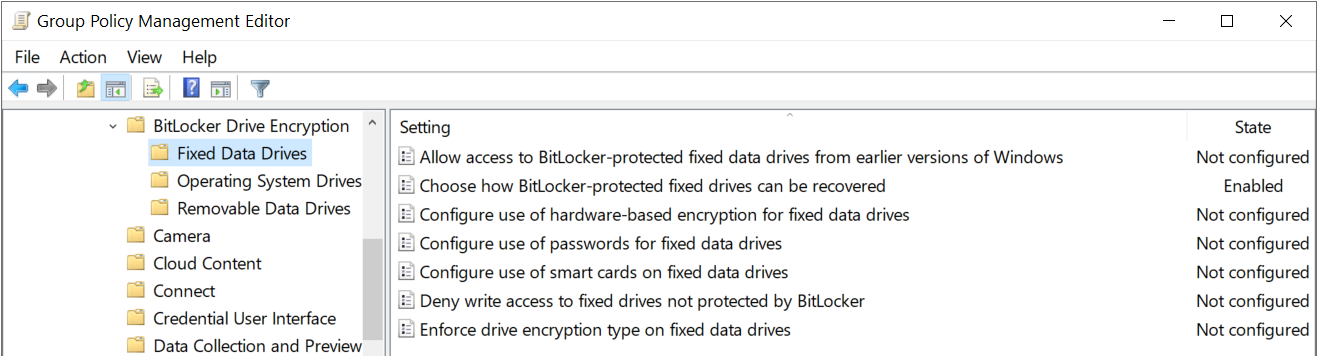
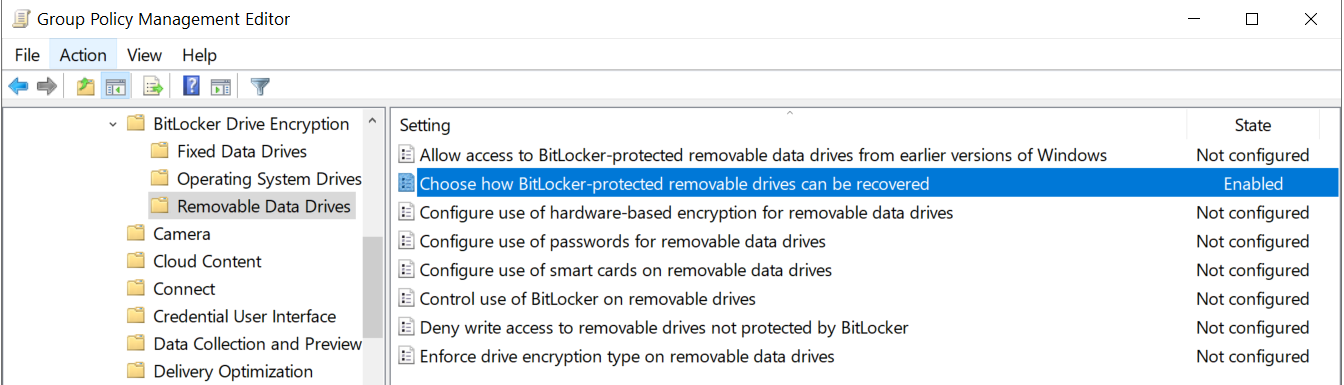
You need to set the option Choose how Bitlocker-protected ### Drives can be Recovered within:
Fixed Data Drives
Removable Data Drives
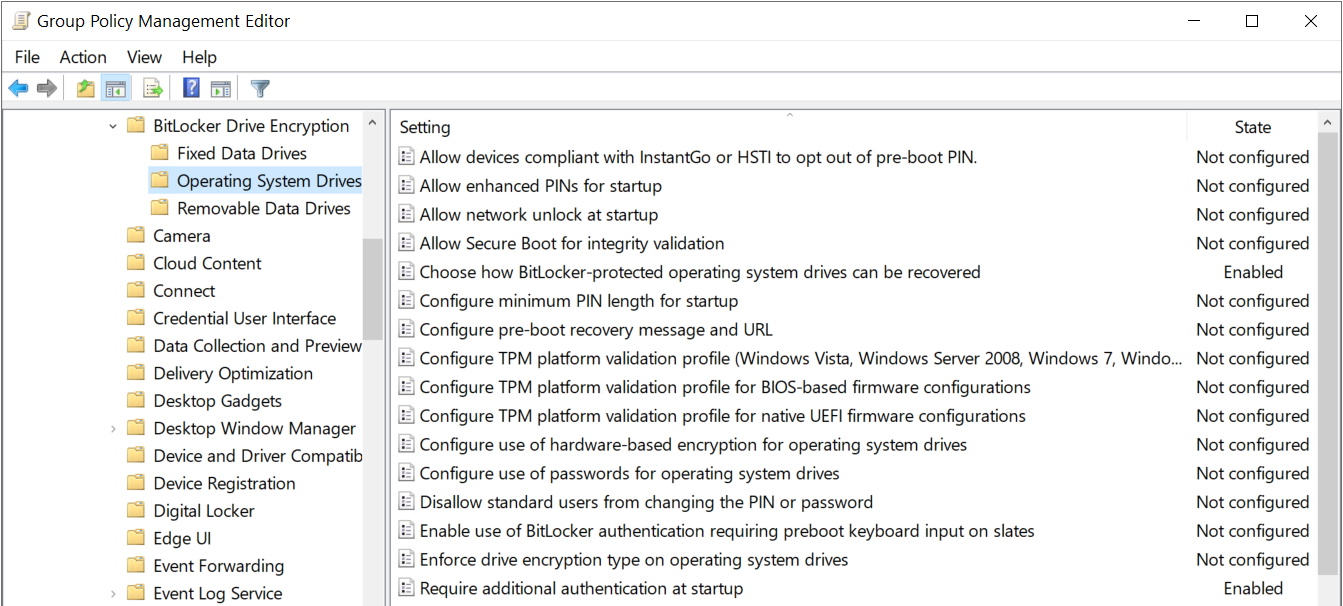
For Operating System Drives you do Exactly the same but as per a previous post on How to Enable Bitlocker without TPM you can also enable the option:
Require additional Authentication at Startup
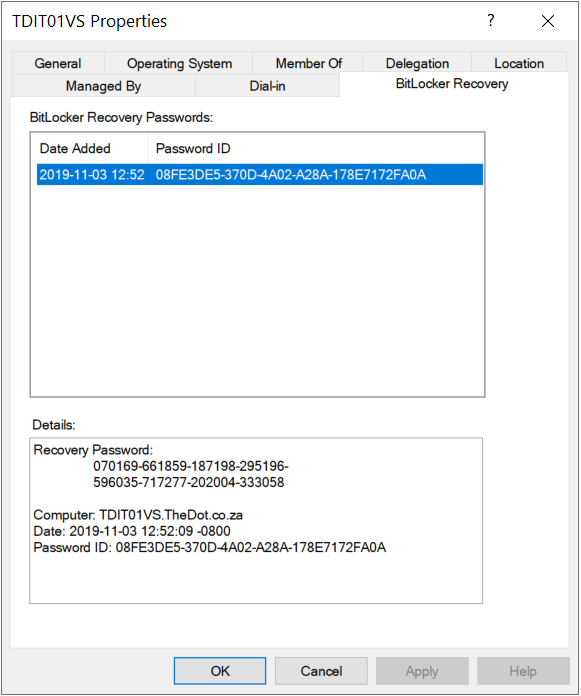
That is it all complete, you can now run a gpupdate on the machine you are enabling Bitlocker on and test. Once done it should look similar as per below.