When working with shared folder we first need to understand the difference between Shared Permissions vs NTFS Permissions.
Look there is many Articles out there what the difference is, for this purposes we just need to know what access it allow.
Shared Permissions

Shared permission only applies to a Folder being accessed over a Network.
There is only three options to choose from:
Full Control, Change and Read.
Full Control
The Users has “Change” permissions including they can change permissions for NTFS Files and Folders
Change
The users has “Read” permission including they can Add Files and Folders, Change data, and delete Files and Folders
Read
The user can view File and Folder names, Read Data and run programs
At this stage when working with NTFS partitions I highly suggest putting the FAT32 Permissions on Full Control and Manage User access on the NTFS side.
In Stating this you need to manage you NTFS Permission accordingly as well, if not you are gonna give yourself a lot of problems down the line.
NTFS Permissions
So NTFS Permissions what makes them so important? Well the Fact that you can control every detail of a users access. I think we need to Quote Spider Man:
With Great Power Comes Great Responsibility – Thanks Marvel. So with Great Control you Comes Great Responsibility.
Lets have a quick Squiz what Microsoft gave us, the Access type

Principal
This is a User or Group that has Access
Type
Allow or Deny Access
Applies to:
To what type of object does this apply
And here we have a combination to choose from: This Folder Only, Subfolder Only, Files Only or if you want a combination of them, This Folder and Sub Folders, This Folders and Folder and Files, Sub Folders and files or by Default you can choose all three This Folder, Sub Folders and Files.
Now we get to Choose what access they have to this specific Object, the NTFS Permissions
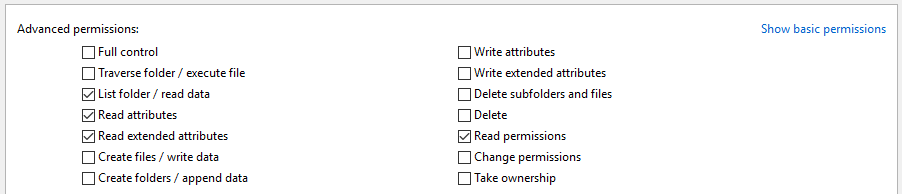
Overwhelming right!!! At least compared to shared permissions.
So let me break it up quickly. For the most part the permission is straight forward what you read is exactly what you are going to get.
For the exception of a few sections that we need to clarify on what it actually means.
Starting with the Sections which is split in two Ex. List Folder / Execute File. Basically anything on the left of “/” is application to the folder and Sub Folders, anything to the right is Files Only.
Then the Difference between Delete Subfolders and files and Delete. Delete refers to the current folder you are changing the permissions on and Delete Sub Folders and Files is then literally the Sub Folders and Files below the current folder.
So in the interest of not skipping anything on the Permissions there is Three options we need to quickly works through.
Firstly when assigning permission you have the option “Only apply these permissions to object and/or containers within the container”
This option is only to be used when you need the direct or first line of Folders and Files to take permissions, it will not duplicate to your Second Tier Folder. It is almost like not having Inheritance turned on for this permission set.
Inheritance
The Second option Inheritance. This tells the Second Tier Folders if it should take the permissions from the First Tier Folder as well as permission you explicitly assign to Second tier folders.
You can also turn of inheritance meaning all changes you make to Tier One folders wont pull through to the specific Tier Two folder.
Let me give you and Example.
If you have a Folder C:\Temp and on this folder the Group Everyone has Full control on the next Folder you create C:\Temp\Restricted the Group Everyone will also have Full control.
On the Folder C:\Temp \Restricted you then want to Deny access for Miss. Tickle. Great now Tess won’t have access to this folder because it looks at both the inherited permissions and the explicit permissions.
Alternatively you can disable the inheritance completely and only give access to the necessary person that needs access, just bare in mind to get to a Second Tier Folder they need access on the previous folder to browse through. So if MR. Conda is granted Full control to C:\Temp\Restricted but has no Access to C:\Temp then he wont be able to access the required Folder. I am so sorry for you Anna.
The Most Dangerous Option
Lastly, I can not stress how Dangerous this Option is only use it if you are absolutely 100% confident you know what you are doing. “Replace all Child Object Permission entries with inheritable permission entries from this object”. People this can destroy hours of work and planning in a single tick mark. There is NO explanation needed. It literally does what is read. Takes the permission from the folder you are currently working on and replaces every permission for every Folder, Sub Folder and File with regardless if inheritance is disable or not.
Allow VS Deny
To Finish of the explanation we need to talk about Allow VS Deny. Rule of Thumb is and Explicit Deny will take precedence over and Allow. This does not mean it will always work I hear of times where and Inherited Deny did not work on folder because of Explicit Allow. Thus we now have the option on the Advance Security window for Effective Permissions, to view access granted. This will help you troubleshoot why a user has delete access when they should not have.
To Read up more about the topic here is link to Microsoft which gives more detail.
So this is the basic’s when it comes to Folder permissions. I hope this helps you understand how to plan your Shared Structure Environment.
Please take your time and understand what your need is before jumping in and creating shared folders all over your Network.
